Specialist Clearweb news sites such as DeepDotWeb and All Things Vice provide news coverage and practical information about dark web sites and services; however, DeepDotWeb was shut down by authorities in 2019. Media coverage typically reports on the dark web in two ways; detailing the power and freedom of speech the dark web allows people to express, or more commonly reaffirms the illegality and fear of its contents, such as computer hackers. Many journalists, alternative news organizations, educators, and researchers are influential in their writing and speaking of the dark web, and making its use clear to the general public. OSINT, or Open Source Intelligence, are data collection tools that legally collect information from public sources. As a result, law enforcement has employed many other tactics in order to identify and arrest those engaging in illegal activity on the dark web. When investigating online suspects, police typically use the IP (Internet Protocol) address of the individual; however, due to Tor browsers creating anonymity, this becomes an impossible tactic.
Both works find out that the business models of these markets is maturing. The current literature on them has covered well various important features, providing valuable insights for the understanding of how dark web markets operate. As rapidly developing business, dark web markets are undergoing changes all the time.
Initially designed for secure military communications, it evolved into a broader tool for online anonymity, later expanding to public use with the Tor network. The dark web presents various threats, including malicious software and computer viruses, posing risks to users' systems and data security. To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web.
- The dark web is simply a part of the internet that requires special tools like the Onion Browser to get access.
- These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites.
- Stolen data sold on a darknet site today can fuel tomorrow’s account takeover breaches and ransomware attacks impacting both individuals and businesses.
- The Nexus team invites you to experience an unforgettable marketplace.
- They also don't shy away from striving toward local domination, which Western darknet market operators avoid "due to the resulting pressure, attention and risk of law enforcement action that such dominance could bring," TRM Labs says.
The internet is a vast and complex space, with many layers that often go unnoticed by the average user. Among these layers lies the darknet, a part of the internet that is not indexed by traditional search engines. While it is often associated with illegal activities, the darknet also serves as a platform for privacy advocates, journalists, and whistleblowers. Understanding how to navigate this hidden aspect of the internet can be crucial for those seeking information or wishing to protect their identity online. In this article, we will explore accessing darknet market and provide insights into its workings.
Accessing Darknet Market
To start with, it’s essential to clarify what a darknet market is. A darknet market is a platform where users can buy and sell goods and services—often anonymously. While many associate these markets with illegal drugs or weapons, they can also host legal products like digital art or privacy tools. To navigate these markets effectively, one must follow specific steps to ensure safety and anonymity.
Step 1: Downloading Necessary Tools
Accessing the darknet typically requires specialized software. Tor (The Onion Router) is the most commonly used browser for this purpose. Tor provides anonymity by routing users’ internet traffic through a series of volunteer-operated servers. This makes it difficult to trace online activity back to the user. Downloading and installing the Tor browser is the first step to accessing darknet market.
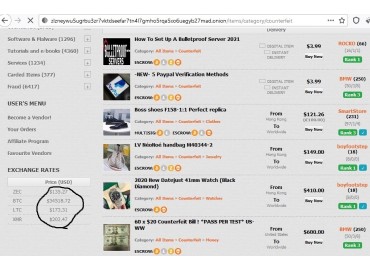
Step 2: Understanding Marketplaces
- A listing for VPN credentials or RDP access to your organization can appear on a marketplace days or weeks before an actual attack occurs.
- Many marketplaces shut down suddenly due to exit scams, where administrators disappear with user funds.
- However, rivalries over dark web marketplaces could also lead to turf wars, disrupting their operations and creating new risks for businesses.
- In February 2015, the EMCDDA produced another report citing the increased importance of customer service and reputation management in the marketplace, the reduced risk of violence and increased product purity.
- It's the internet you see and use every day and consists of all the websites indexed by traditional search engines like Google.
- Social media platforms like Facebook and news sites like the BBC and ProPublica have also waded into the dark web’s waters.
Once the Tor browser is installed, users can begin exploring various darknet markets. It’s crucial to conduct thorough research on different platforms before making any transactions. Some popular darknet markets include Silk Road and AlphaBay, though their status can change frequently due to law enforcement actions. Always seek out current forums or resources that provide updated lists of operational darknet markets.
Step 3: Ensuring Anonymity
Maintaining security and anonymity is vital when accessing darknet market. Here are a few tips to enhance your privacy:
- Use a Virtual Private Network (VPN) alongside the Tor browser.
- Create pseudonymous accounts, using unique usernames that do not tie back to your real identity.
- Avoid sharing personal information or engaging in discussions that could reveal your identity.
Step 4: Making Transactions
Darknet markets primarily use cryptocurrencies for transactions due to their anonymity features. Bitcoin is the most common form, but other cryptocurrencies like Monero offer enhanced privacy features. Users should familiarize themselves with setting up a cryptocurrency wallet before attempting to make purchases. Remember, all transactions come with risks, so double-check vendor reputations and reviews from previous buyers.

Step 5: Navigating Risks
While accessing darknet market has its advantages, it’s crucial to acknowledge the inherent risks. Law enforcement agencies monitor these platforms, so users must remain cautious. Avoiding any illegal activities is paramount, and being aware of potential scams is equally important. Knowledge about the marketplace and its environment is your best defense against fraud.
Conclusion
In summary, accessing darknet market can provide a wealth of information and resources. However, safety should always be a priority. By taking the necessary precautions and understanding the intricacies of the darknet, users can protect their identity and navigate this hidden section of the internet more effectively. Whether for research, privacy, or legitimate goods, education is key to making informed decisions in the complex world of the darknet.