In today's digital age, the internet offers a vast landscape of information and services, some of which exist beyond the reach of the traditional web. Among these hidden corners lies a world known as the darknet, where markets operate outside conventional regulations. Understanding how to access darknet markets can be crucial for individuals seeking privacy, anonymity, or alternative products and services. This article aims to elucidate how these markets function, the precautions one should take, and the ethical considerations involved.
- Still, the Tor dark web browser also remains a vital tool for privacy-conscious users.
- Rather than focusing on current availability, we examined overall impact and relevance within broader darknet discussions.
- In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the "Marco Polo" darknet market.
- No investigator can know all there is to know about every single marketplace.
In contrast, darknet markets operate in the shadows, making them more vulnerable to fraud, theft, and other forms of criminal activity. While traditional markets are not immune to crime, they are generally well-lit, populated, and monitored, which can discourage criminal behavior. Traditional markets also offer a sense of community and social interaction that is lacking in darknet markets. In contrast, darknet markets operate on fixed prices, with little to no room for negotiation.
- Any time the information-stealing malware detected changes to a victim’s passwords or a new account, it would update the Genesium browser with the latest credentials.
- Without knowing which forums matter, which threats are credible, or how to interpret hacker chatter, browsing accomplishes little.
- Common items for sale include credit card data, credentials, and even fingerprints.
- Stealer logs are packages of data stolen by malware from infected computers.
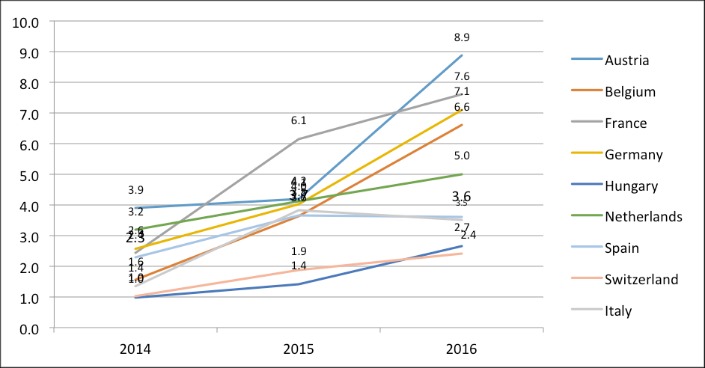
- To observe the behavior of the ecosystem on specific calendar periods, such as weekly or quarterly, we select a time period and aggregate the daily time series through step 3 accordingly.
Access Darknet Markets
What are Darknet Markets?
Darknet markets are online platforms that facilitate the buying and selling of goods and services, often illicit in nature. These markets are only accessible through specialized software, most commonly Tor, which provides anonymity for its users. While they are frequently associated with illegal activities, such as drug trafficking and weapon sales, there are also legitimate uses for privacy-minded individuals.
How to Access Darknet Markets Safely
To access darknet markets safely and securely, follow these essential steps:
- Install Privacy-Focused Software: Download and install the Tor browser, which allows users to access .onion sites exclusive to the darknet. This software anonymizes your internet connection.
- Utilize a VPN: While the Tor network adds a layer of anonymity, using a virtual private network (VPN) can provide additional security by masking your IP address and encrypting your internet traffic.
- Be Mindful of Scams: Darknet markets can be rife with scams. Always conduct thorough research on vendors before making transactions to ensure their legitimacy.
- Use Cryptocurrency: Transactions on darknet markets typically use cryptocurrencies like Bitcoin. Familiarize yourself with how to securely purchase and store cryptocurrency.
- Stay Informed: Keep up to date with news and developments related to darknet markets. Awareness of current trends and the potential risks can enhance your safety.
Understanding the Risks
While accessing darknet markets can provide unique opportunities, it is essential to acknowledge the inherent risks involved. Legal repercussions, scams, and exposure to harmful content are significant concerns. Engaging in illegal activities can lead to severe outcomes, including arrest and prosecution. As such, individuals should critically assess the necessity of engaging with these markets and consider the implications of their actions.
Ethical Considerations
The ethics surrounding darknet markets often spark debate. While some argue that these platforms promote free speech and privacy rights, others raise concerns about their role in facilitating crime and harm. It is crucial to discern your motivations and the potential impact of your choices. Consider whether your actions align with your values and the ethical implications they may carry.
Conclusion
In summary, while the ability to access darknet markets can be appealing for various reasons, it necessitates an understanding of the associated risks and ethical dilemmas. Responsible engagement, informed decision-making, and prioritizing safety can help navigate this complex digital realm. Always remember to stay vigilant and prioritize ethical considerations in your online activities.